SSL Certificate and private passphrase
 Mia Lopez
Mia Lopez 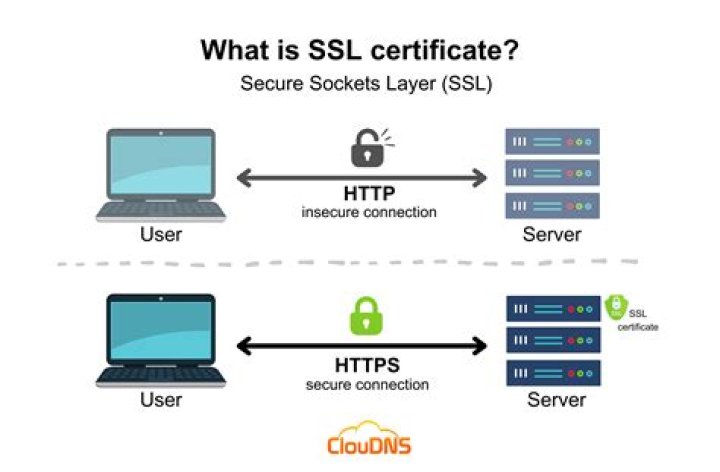
So I have got a weblogic based system which uses 2048-bit key based certificate from Globalsign. The certificate is close to expiring so I got a new certificate from the same vendor (all text which is what I can encode into CER format).
Problem is that this time they have not given me any private passphrase. I took it up with their customer support and they are saying that their process changed and I should be able to get it generated from their certificate and CSR I sent them.
I do not know how to. They calmly referred me to customer support of the weblogic vendor (i.e. Oracle) and bailed out. Past interaction with Oracle customer support have created more problems that it solved.
Any help would be appreciated. Also I tried these links, did not help:
PKI Certificate Authority private a keys and certificates
Get RSA private key and certificate from GlobalSign certificate
2 Answers
First, certificates consist entirely of public information and do not have passphrases. It's "private keys" which may have one.
Second, the CA does not have your private key nor its passphrase – both were generated on your system, because they were used to make the CSR that you submitted. So if you used WebLogic to generate the CSR, that likely means it already has the private key stored and is just waiting for the certificate to be imported alongside it (at least that's how it works in most other programs).
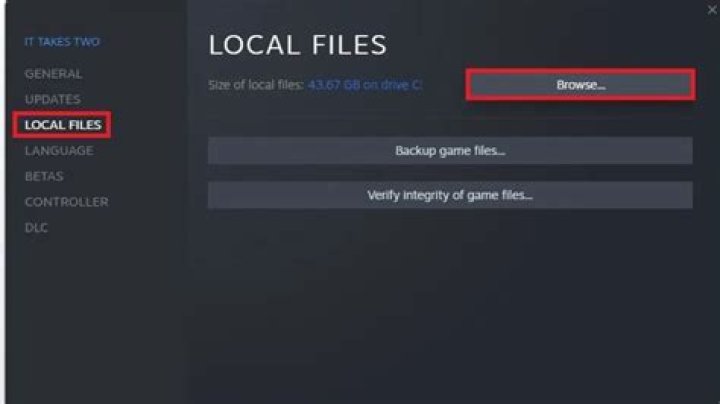
If you used Java keytool to generate the CSR, then the private key is stored in the Java keystore file (if you did not specify a custom path, it'll be at ~/.keystore). To extract keys from Java keystore into a PEM format:
Use
keytool -listto make sure it shows your key and to check the keystore format. If it's PKCS12, skip to step 3.If you have a JKS format keystore, convert it to PKCS12 format using:
keytool -importkeystore -srckeystore <old_path> -destkeystore <new_path> -deststoretype PKCS12Once you have a PKCS12 keystore, use
opensslto export its contents to PEM format files:openssl pkcs12 -in <old_path> -out <new_path> -nodes
The Certificate Signing Request is very similar to a self-signed cert; it acts as proof that you have the key, but the key itself never leaves your system. The CA just transforms your provided CSR into a real certificate and returns it. At all stages, the certificate or CSR consists entirely of public information and is never passphrase-protected.
As far as I know, WebPKI CAs (such as GlobalSign) are actually forbidden by CA/B Forum rules from generating private keys for a customer and are required to revoke certificates if the private key is "leaked".
6Thanks for all your help. I was getting confused unnecessarily. The SSL vendor provided Java PKCS file with a password. I got confused between password, passphrase and keystore passphrase. This time we got CSR only, so that was the confusion.