sshd ignoring PermitRootLogin directive
 Mia Lopez
Mia Lopez 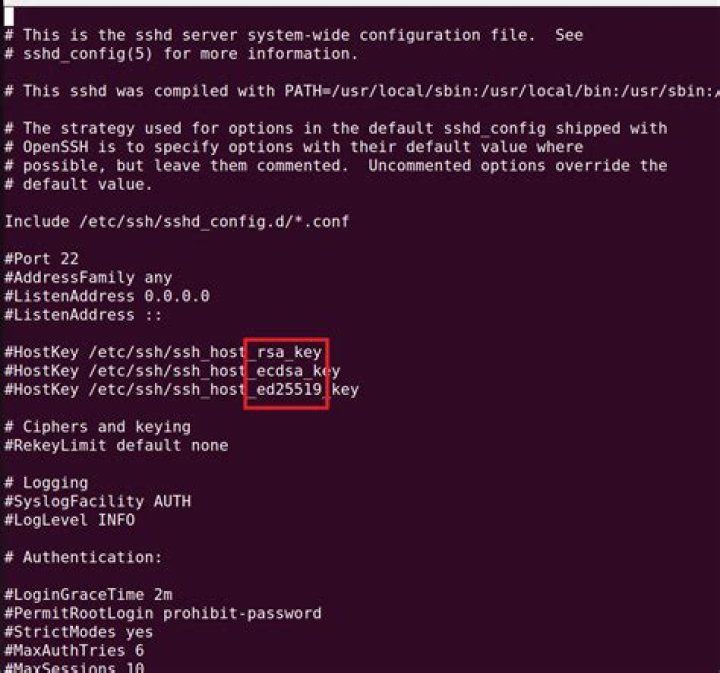
After setting PermitRootLogin no and restarting the sshd service, I'm still presented with a password prompt when logging in as root.
This is Ubuntu MATE 16.04 running OpenSSH 7.2p2-4 (up-to-date as I write this):
lgr@rpi-lgr13-0199:~$ uname -a
Linux rpi-lgr13-0199 4.4.38-v7+ #938 SMP Thu Dec 15 15:22:21 GMT 2016 armv7l armv7l armv7l GNU/Linux
lgr@rpi-lgr13-0199:~$ apt-cache policy openssh-server
openssh-server: Installed: 1:7.2p2-4ubuntu2.8 Candidate: 1:7.2p2-4ubuntu2.8 Version table: *** 1:7.2p2-4ubuntu2.8 500 500 xenial-updates/main armhf Packages 500 xenial-security/main armhf Packages 100 /var/lib/dpkg/status 1:7.2p2-4 500 500 xenial/main armhf PackagesMy server is configured with PermitRootLogin no and has been restarted (many times) to make the change effective:
Worth noting I've only restarted the service, not the machine (it's in production).
lgr@rpi-lgr13-0199:~$ sudo systemctl status sshd.service
● ssh.service - OpenBSD Secure Shell server Loaded: loaded (/lib/systemd/system/ssh.service; enabled; vendor preset: enabled) Active: active (running) since Wed 2019-10-30 11:53:20 PDT; 9min ago Process: 6680 ExecReload=/bin/kill -HUP $MAINPID (code=exited, status=0/SUCCESS) Process: 6674 ExecReload=/usr/sbin/sshd -t (code=exited, status=0/SUCCESS) Process: 8187 ExecStartPre=/usr/sbin/sshd -t (code=exited, status=0/SUCCESS) Main PID: 8191 (sshd) CGroup: / └─8191 /usr/sbin/sshd -D
Oct 30 11:53:20 rpi-lgr13-0199 systemd[1]: Starting OpenBSD Secure Shell server...
Oct 30 11:53:20 rpi-lgr13-0199 sshd[8191]: Server listening on 0.0.0.0 port 22.
Oct 30 11:53:20 rpi-lgr13-0199 sshd[8191]: Server listening on :: port 22.
Oct 30 11:53:20 rpi-lgr13-0199 systemd[1]: Started OpenBSD Secure Shell server.
lgr@rpi-lgr13-0199:~$ last boot
wtmp begins Tue Oct 1 12:41:27 2019
lgr@rpi-lgr13-0199:~$ sudo ls -l /etc/ssh/sshd_config
-rw-r--r-- 1 root root 2562 Oct 22 09:11 /etc/ssh/sshd_config
lgr@rpi-lgr13-0199:~$ sudo ls /root/.ssh
known_hosts
lgr@rpi-lgr13-0199:~$ cat /etc/ssh/sshd_config | grep PermitRootLogin
#PermitRootLogin prohibit-password
PermitRootLogin no
# the setting of "PermitRootLogin without-password".
lgr@rpi-lgr13-0199:~$ sudo sshd -T | grep root
permitrootlogin noUsing sudo /etc/init.d/ssh restart instead of sudo systemctl restart sshd.service has no effect. I am still able to attempt password-based login and my failed attempts show up in the normal logs:
pokeeffe@airtech ~
λ ssh -v root@myserver
OpenSSH_7.6p1, OpenSSL 1.0.2n 7 Dec 2017
debug1: Reading configuration data /c/Users/pokeeffe/.ssh/config
debug1: Reading configuration data /etc/ssh/ssh_config
debug1: Connecting to myserver [<REDACTED>] port 22.
debug1: Connection established.
debug1: identity file /c/Users/pokeeffe/.ssh/id_rsa type 0
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_rsa-cert type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_dsa type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_dsa-cert type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_ecdsa type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_ecdsa-cert type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_ed25519 type -1
debug1: key_load_public: No such file or directory
debug1: identity file /c/Users/pokeeffe/.ssh/id_ed25519-cert type -1
debug1: Local version string SSH-2.0-OpenSSH_7.6
debug1: Remote protocol version 2.0, remote software version OpenSSH_7.2p2 Ubuntu-4ubuntu2.8
debug1: match: OpenSSH_7.2p2 Ubuntu-4ubuntu2.8 pat OpenSSH* compat 0x04000000
debug1: Authenticating to myserver:22 as 'root'
debug1: SSH2_MSG_KEXINIT sent
debug1: SSH2_MSG_KEXINIT received
debug1: kex: algorithm:
debug1: kex: host key algorithm: ecdsa-sha2-nistp256
debug1: kex: server->client cipher: aes128-ctr MAC: compression: none
debug1: kex: client->server cipher: aes128-ctr MAC: compression: none
debug1: expecting SSH2_MSG_KEX_ECDH_REPLY
debug1: Server host key: ecdsa-sha2-nistp256 SHA256:U4PTRxit9wtLrQVMF7BIwZk+TlgoT3RmT2GqJnBcL1g
debug1: Host 'myserver' is known and matches the ECDSA host key.
debug1: Found key in /c/Users/pokeeffe/.ssh/known_hosts:61
debug1: rekey after 4294967296 blocks
debug1: SSH2_MSG_NEWKEYS sent
debug1: expecting SSH2_MSG_NEWKEYS
debug1: SSH2_MSG_NEWKEYS received
debug1: rekey after 4294967296 blocks
debug1: SSH2_MSG_EXT_INFO received
debug1: kex_input_ext_info: server-sig-algs=<rsa-sha2-256,rsa-sha2-512>
debug1: SSH2_MSG_SERVICE_ACCEPT received
debug1: Authentications that can continue: publickey,password
debug1: Next authentication method: publickey
debug1: Offering public key: RSA SHA256:XPYfeIOamEPN2i7D/NKKLthIac3KGj8npWGyJG7Q3XI /c/Users/pokeeffe/.ssh/id_rsa
debug1: Authentications that can continue: publickey,password
debug1: Trying private key: /c/Users/pokeeffe/.ssh/id_dsa
debug1: Trying private key: /c/Users/pokeeffe/.ssh/id_ecdsa
debug1: Trying private key: /c/Users/pokeeffe/.ssh/id_ed25519
debug1: Next authentication method: password
root@myserver's password:
debug1: Authentications that can continue: publickey,password
Permission denied, please try again.
root@myserver's password:Oct 30 12:41:29 rpi-lgr13-0199 sshd[11980]: Failed password for root from <REDACTED> port 63841 ssh2
Oct 30 12:41:29 rpi-lgr13-0199 sshd[11980]: Connection closed by <REDACTED> port 63841 [preauth]This doesn't seem correct at all based on documentation and experience. What am I doing wrong? Or is this a known issue?
51 Answer
It all looks normal to me. You cannot login as root.
ssh behaves as it should. Only if you entered the right credentials would the option come into play.
Not allowed to log in does not mean not allowed to try...
PermitRootLogin Specifies whether root can log in using ssh(1). The argument must be yes, prohibit-password, forced-commands-only, or no. The default is prohibit-password. If this option is set to prohibit-password (or its deprecated alias, without-password), password and keyboard-interactive au‐ thentication are disabled for root. If this option is set to forced-commands-only, root login with public key authentication will be allowed, but only if the command option has been specified (which may be useful for taking remote backups even if root login is normally not allowed). All other authentication methods are disabled for root. If this option is set to no, root is not allowed to log in.


