Linux tells me a serial port is in use, but it isn't
 Andrew Mclaughlin
Andrew Mclaughlin 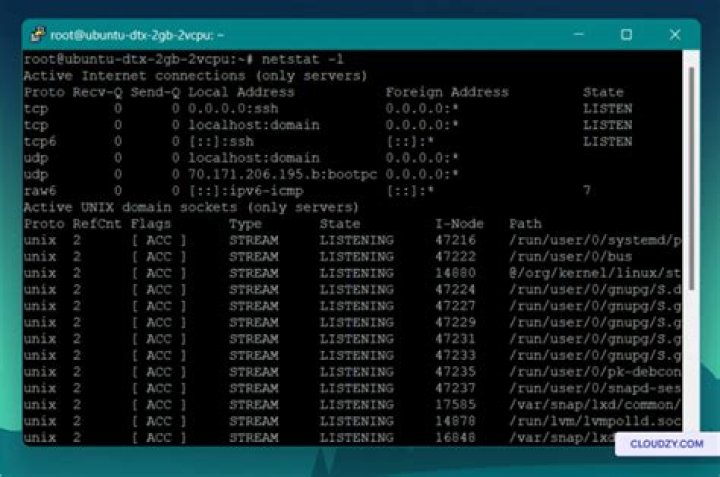
On CrunchBang linux (Debian variant), I have a COM port on ttyS0, which I'm trying to use with an NFC device. libnfc responded that it couldn't see any NFC devices, so I tried directly opening the COM port. For this, I used:
sudo cu -l /dev/ttyS0 -s 9600However, this command returns:
cu: open (/dev/ttyS0): Permission denied
cu: /dev/ttyS0: Line in useI don't know what could possibly be using this connection. To find out, I've tried reading all open processes and filtering for the use of ttyS0:
ps -ef | grep ttybut for this command, nothing shows up that is using ttyS0. I've also tried grabbing all open files and filtering for a lock on ttyS0:
lsof | grep ttybut this returns nothing using ttyS0.
How is it possible the cu says the line is in use, but both ps and lsof return nothing using that line?
4 Answers
There is probably no real usage of the line, but a permission issue. quick and dirty way to test for me was to execute:
ls -la /dev/ttyUSB0
sudo chmod 666 /dev/ttyUSB0and retry cu. If it starts working, you need to take care of the respective udev file and the user permissions/groups. For my device it looked like this (being member in plugdev group):
> cat /etc/udev/rules.d/42-CP210x.rules
ATTRS{idVendor}=="10c4", ATTRS{idProduct}=="ea60", SUBSYSTEMS=="usb",
ACTION=="add", MODE="0666", GROUP="plugdev"Serial devices privileges are granted to members of the dialout group. To get connected to /dev/ttyS0 I added the current user to the group using:
sudo adduser <username> dialout
It seems that this is a bug in cu. I solved this by changing owner group of /dev/ttyUSB0 using following command:
chown root:root /dev/ttyUSB0Add your user to the dialout group. Depending on the system, it may also be necessary to add your user to the uucp group.
Check the group for membership:
getent group dialoutOr check your user:
groups `whoami`Add your user if necessary:
usermod -aG dialout `whoami`verify with getent as mentioned above.