IPv6 does not work over bridge
 Matthew Martinez
Matthew Martinez 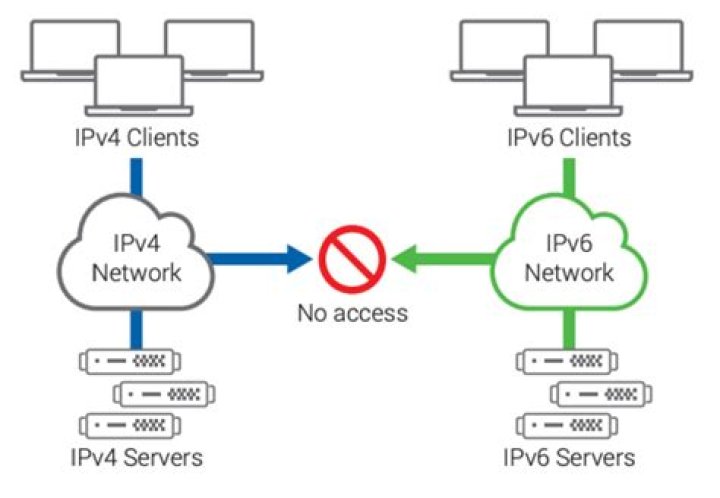
I installed Ubuntu 14.04 server a week ago. I use it as a virtual machine host (tasksel installed). meaning am running it with kvm + libvirt.
I have set up the same bridge I had in 13.10.
auto p4p1
iface p4p1 inet manual up ifconfig $IFACE up down ifconfig $IFACE down
auto br0
iface br0 inet static address 46.182.xxx.xxx netmask 255.255.255.240 gateway 46.182.xxx.xxx dns-nameservers 46.182.xxx.xxx 46.182.xxx.xxx bridge_ports p4p1 bridge_stp off bridge_maxwait 0
iface br0 inet6 autoAgainst br0 I connect my virtual machines with <source bridge='br0'/> defined in libvirt.
My virtual machines get Router Advertisement messages without problem. All virtual machines get IPv6 addresses.
My problem is that IPv6 does not work over the bridge. But it does work when I turn on tcpdump against br0 for troubleshooting. I have tried setting the interface manually into promiscous mode but that does not make it work, ifconfig br0 promisc.
Why I have the IPv4 addresses on the bridge? I do not know, old habit, never question it. IPv6 does not work on the virtual machine host but the host get IPv6 address by RA, just like the virtual machines.
83 Answers
Every IPv6 address, even link-local ones, automatically subscribe to a multicast group based on its last 24 bits. If multicast snooping is enabled, the bridge filters out (almost) all multicast traffic by default. When an IPv6 address is assigned to an interface, the system must inform the network that this interface is interested in that particular multicast group and must be excluded by the filter. The following is a good introductory video:
Multicast snooping is there to prevent flooding the network with multicast packets that most systems aren't interested. You can disable multicast snooping in small deployments without noticing any big difference. But this may have significant performance impact on larger deployments.
You can disable snooping with:
echo -n 0 > /sys/class/net/<brif>/bridge/multicast_snoopingIf you want to protect your VMs from unwanted traffic and unnecessary packet processing, you can leave snooping enabled but also enable a multicast Querier on the network. A Querier will periodically broadcast query packets and update snooping filters on switches and bridges. It is possible to enable a Querier on your system with:
echo -n 1 > /sys/class/net/<brif>/bridge/multicast_querierIf you have snooping enabled, you must also have a querier on the network.
There's no need to enable STP. It's probably safer to turn it off, unless you know that you're bridging segments that result in circular paths. It's also irrelevant if you have SLAAC enabled (ie autoconf=1, accept_ra=1). Enabling PROMISC mode on the bridge implicitly disables snooping.
Here's a nice summary of the modern challenges of IPv6 Neighbor Discovery (ND) and Multicast Listener Discovery (MLD).
have you enabled IPv6 on the interface at all? if the bridge device is br0, then do this:
sysctl net.ipv6.conf.br0.disable_ipv6=0
sysctl net.ipv6.conf.br0.autoconf=1
sysctl net.ipv6.conf.br0.accept_ra=1
sysctl net.ipv6.conf.br0.accept_ra_defrtr=1The only obvious problem I see with your configuration is:
bridge_stp offFor various reasons STP needs to be enabled on libvirt bridges.
Change the configuration to:
bridge_stp onYou can also activate it immediately without restarting the network:
$ sudo brctl stp br0 on