How to ssh a computer which is behind firewall
 Olivia Zamora
Olivia Zamora 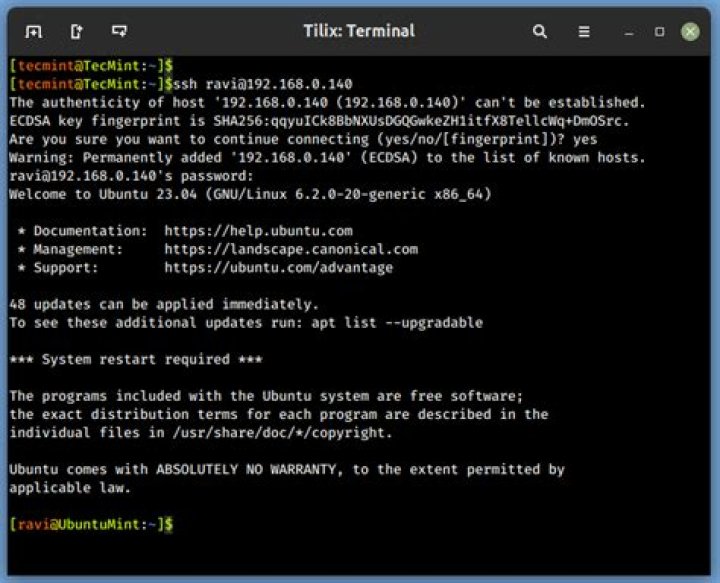
Consider I have three computers
homemy computer at homeworkmy computer at workservermy server
I can't connect from home to work using ssh because of my company firewall. But I can ssh any computer from work. For example I can ssh the server computer from work. What I wan't to do is to connect to Internet using the work connection (I want to access localhost of the work computer). I read from some toturial that I can do:
woork:~# ssh -D 4096 serverBut this only allow me to connect to the Internet using the server. I want to do the inverse of this but I can't access work from server.
The final result is to open firefox at home and browse to localhost of work.
What's the solution for my case?
72 Answers
If you can set up an outgoing ssh connection, then you can probably set up a reverse tunnel to get back in (I'm not aware of there being a way for IT to forbid this, but you never know).
work:~# ssh -fN -R 2222:localhost:22 serverThen on the server you can do this:
server:~# ssh -p2222 localhostAnd you will magically be connected back to the SSH server port on you work machine. By default the port 2222 is bound to the "localhost" address only, so connect requests from home will not work:
home:~# ssh -p2222 server ;# this will not workInstead, you can do this:
home:~# ssh server
server:~# ssh -p2222 localhostor both in one command like this:
home:~# ssh -o ProxyCommand="ssh -W localhost:2222" serverTo make all this easier to live with, add this to your .ssh/config at home:
Host work ProxyCommand ssh -W localhost:2222 HostName server... and now:
home:~# ssh work... will just do the right thing.
It is possible to create the reverse tunnel bind so that the proxy business is not necessary, but then every hacker in the world will also pound on your tunnel (thinking port 2222 is non-standard and therefore safe is naive). The failed access attempts will show up in the logs on "work", IT will find out, and you'll get fired. Of course, the tunnel alone is probably a firing offence, but there's no need to make it obvious.
3Suppose you have
work:~#
home:~#And work:~# is the firewall you can't control
When you write server, I see from context (ssh -D 4096 server), that you mean SSH server. (and not e.g. VNC server). You should specify really, it's clearer. Normally if you have an SSH server it'd be on either work or home. It should be on the computer with the firewall that you can control, that is, Home.
You'd also typically have a regular server that you want to reach, and that's normally not an SSH server. Though it can be, there's a question with a great example of where one might want it to be.
Perhaps you can explain more what server:~# is, but i'm going to skip it out in the meantime 'cos it seems unncecessary and it's not clear what you mean by it 'cos if you have an SSH server e.g. on work then you'd get a prompt work:~#
So what you do is
From the one you can't control i.e. work, you make an outgoing connection. 'cos the firewall lets them out.
home:~# START VNC server on e.g. 5901
home:~# START SSHD SERVER on e.g. port 80 <-- whatever the command is to start your sshd.
work:~# ssh -R 1234:127.0.0.1:5901 user@homeip -p 80
home:~# vncviewer 127.0.0.1:1234 Home sees work.
really the switches to know for SSH are -L, -R and -D
And if you are connecting the client program to the listening port in such a way that the client program is on a different machine to your listening port, then it needs to be -R *:1234:127.0.0.1:5901 or 0.0.0.0:1234:127.0.0.1:5901
Though bear in mind, that's for something like VNC, but if you did it for HTTP you'd only be able to view one site. There is -D which as you see is local.
Some people are at home and want to access a server at work, and that server is behind a firewall they don't control.
But if you want internet access, then you're at work, wanting to access a server at home..
Why on earth can't you do that?
Try running the SSHD server on port 80 or port 443 at home, and do work~:#ssh homeip -p 443