How to enable IPTABLES tracing on ubuntu 18.04 server
 Sebastian Wright
Sebastian Wright 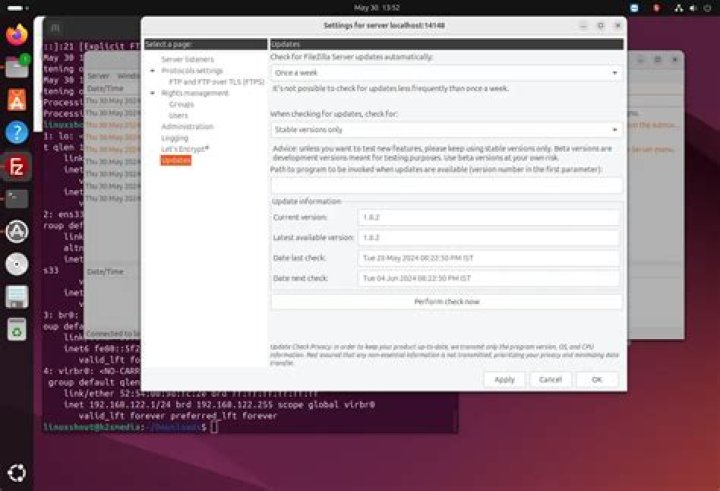
Ive found this simple straightforward way to trace what Iptables is doing on my kubernetes/calico cluster
Nor ipt_LOG, neither xt_LOG output setting is working for me
root@xxx:/var/log# sysctl -w net.netfilter.nf_log.2="ipt_LOG"
sysctl: definição da chave "net.netfilter.nf_log.2": Arquivo ou diretório inexistente
net.netfilter.nf_log.2 = ipt_LOGWhile writing this question, found out this answer.
Looks like newer kerners use another path
You need to perform the following preparations:
Load the (IPv4) netfilter log kernel module:
# modprobe nf_log_ipv4
Enable logging for the IPv4 (AF Family 2):
# sysctl net.netfilter.nf_log.2=nf_log_ipv4
reconfigure rsyslogd to log kernel messages (kern.*) to /var/log/messages:
# cat /etc/rsyslog.conf | grep -e "^kern"
kern.*;*.info;mail.none;authpriv.none;cron.none /var/log/messages
restart rsyslogd:
# systemctl restart rsyslog
Now check the raw tables – you’ll see that there are already entries coming from firewalld:
# iptables -t raw -L
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
PREROUTING_direct all -- anywhere anywhere
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
OUTPUT_direct all -- anywhere anywhere
Chain OUTPUT_direct (1 references)
target prot opt source destination
Chain PREROUTING_direct (1 references)
target prot opt source destination
We’ll want to add our tracing rules before the existing rules. In this example we’ll trace everything related to HTTP (port 80)
# iptables -t raw -j TRACE -p tcp --dport 80 -I PREROUTING 1
# iptables -t raw -j TRACE -p tcp --dport 80 -I OUTPUT 1