GitHub Actions error: No OpenIDConnect provider found in your account for https://token.actions.githubusercontent.com
 Olivia Zamora
Olivia Zamora 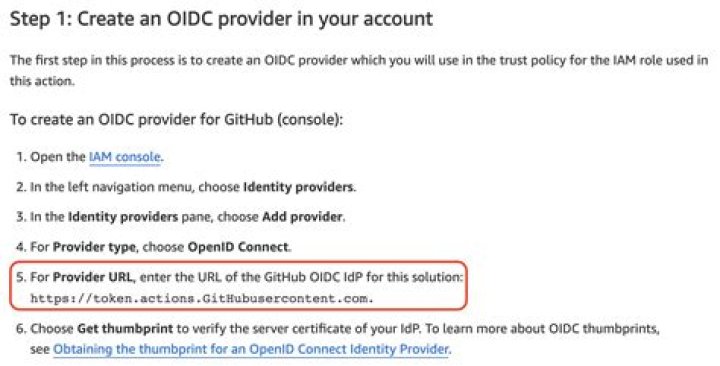
Here is the relevant portion of the yml file I'm using for GitHub Actions:
jobs: AssumeRoleAndCallIdentity: runs-on: ubuntu-latest steps: - name: Git clone the repository uses: actions/checkout@v3 - name: Configure AWS credentials uses: aws-actions/configure-aws-credentials@v1 with: role-to-assume: ${{ secrets.AWS_ROLE_ARN }} role-session-name: GitHub_to_AWS_via_FederatedOIDC aws-region: ${{ secrets.AWS_REGION }}This results in the following error in the GitHub Actions console:
Run aws-actions/configure-aws-credentials@v1
Error: No OpenIDConnect provider found in your account for However, I DO have an OpenIDConnect provider configured in AWS for token.actions.githubusercontent.com, and I have associated that identity provider in a trust relationship with the Role I'm using.
What could the problem be?
1 Answer
Turns out Identity Providers in AWS IAM are case sensitive! My Identity Provider was named like token.actions.GitHubusercontent.com because I copypasta'd from the AWS documentation for connecting GitHub Actions to AWS (see screenshot below).
This doesn't work because it has different casing than what is expected by GitHub, which is token.actions.githubusercontent.com.