Does having an SSL certificate make ssh/sftp connections any more automatic?
 Olivia Zamora
Olivia Zamora 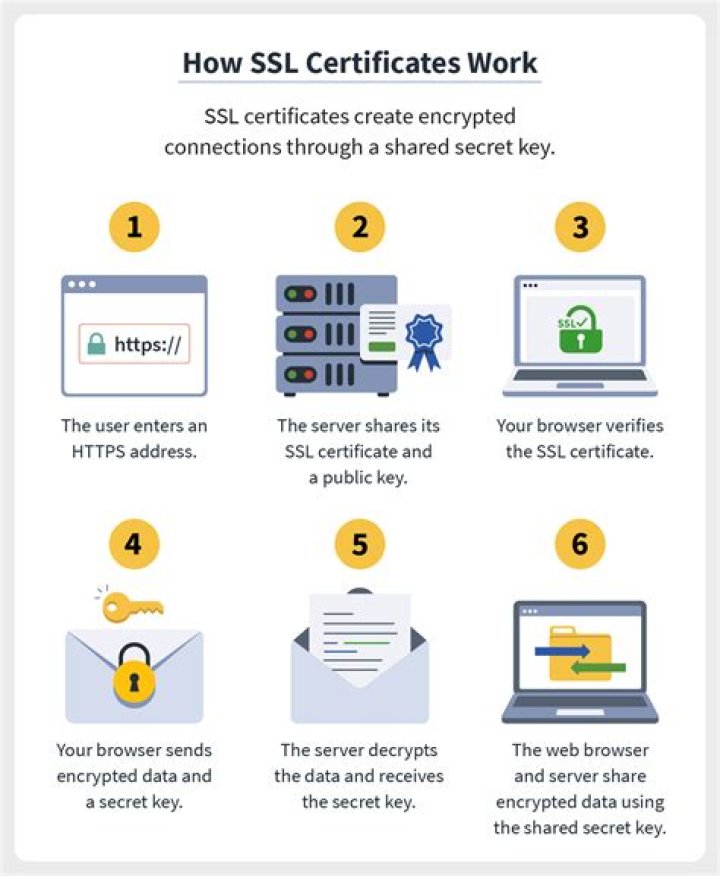
When I log in to a new machine (or from a new machine) using ssh/sftp, I get prompted with the "here's this random string of hex digits; should I trust it?" question. And, since I never have the right stuff in front of me to figure out whether or not the signature is good, I typically think about the network in use and decide accordingly -- perhaps going as far as accepting the signature without actually logging in and then comparing it to what-should-be-the-same signatures found on other machines/logins .ssh directories.
If I get an SSL certificate for my "new" destination machine (say, one of the $4.99 ones from one of the many vendors around the web), can I use that to make the process any more secure/painless (like, would the "do you want to trust that this machine is who it says it is" prompt disappear)? Or are the two (SSL and ssh/sftp) completely disjoint?
1 Answer
No, SSH does not use the SSL protocol, nor X.509 certificates.
Besides, even if it did, you would need to log in over SSH to install a SSL certificate to your server, which would defeat the whole point – at least in the "when I log in to a new machine" case.
If you frequently set up new servers, write a script that would query a given server's fingerprint from multiple different locations (for example, using pssh and ssh-keyscan). If all locations see the same fingerprint, then you're fine.
If you frequently connect from untrusted computers, pick one of your servers to act as a "gateway", write down its fingerprint, and carry it in your wallet/phone/whatever; then make all connections only through that server.
Side note: OpenSSH 6.x does have its own certificate format, but it does not integrate with the existing X.509 PKI and only supports one level of "authorities", so it's only useful when connecting to already-set-up servers from an already-configured client.
The same downside – the need for explicit configuration – also applies to OpenSSH's support for verifying fingerprints over DNSSEC.
Finally, there do exist a few patches for using X.509 within SSH – one used by US DoD, one used by Globus Toolkit (GSI-SSH), possibly others – but they all have the exact same problems as above: it only becomes more automatic when deployed in large organizations. Trying to set up GSI-SSH at home wouldn't save you any time, only waste more of it.