Access Denied while sending email from AWS SES in Lambda function
 Matthew Harrington
Matthew Harrington 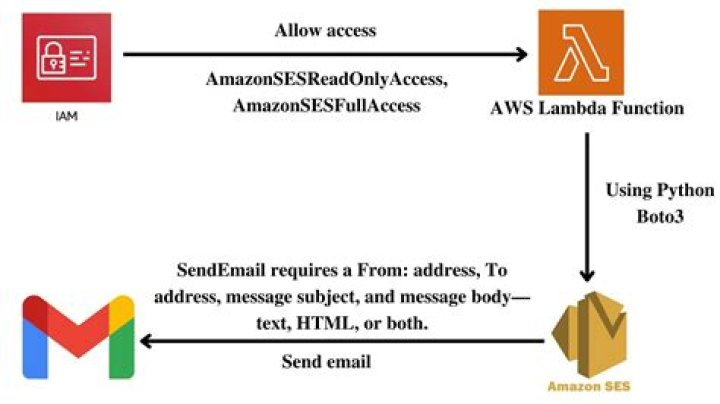
I am trying to send an email using Amazon SES in AWS Lambda function, For this i am facing the following error.
AccessDenied: User
arn:aws:sts::XXXXX:assumed-role/lambda_basic_execution/awslambda_XXXX' is not authorized to performses:SendEmail' on resource `arn:aws:ses:us-west-2:XXX:identity/'
I have granted permission for
3"ses:SendEmail", "ses:SendRawEmail" for the IAM role.
8 Answers
So, I was also having the same problem which Rakesh has explained but couldn't understand the steps he was saying to do so here is a detailed explanation with steps.
You need to do the following Security, Identity & Compliance -> IAM -> Roles -> select your lambda function -> then edit policy -> open it in JSON and add the below part
{ "Effect":"Allow", "Action":[ "ses:SendEmail", "ses:SendRawEmail" ], "Resource":"*"
}or you can do as per requirement from these policy examples also, you need to verify the email address first so don't forget that. Hope this helps everyone.
0After a long debugging i got the issue, "lambda_basic_execution" role need to be granted with permission to access "ses:SendEmail", "ses:SendRawEmail".
Where i was trying to grant permission for the new IAM role i have created, but lambda function is mapped to "lambda_basic_execution" so there is a mismatch.
Reference -
1If you are configuring policies for a SAM Lambda or using a YAML configuration file, you would use something like this:
template.yaml
AWSTemplateFormatVersion: '2010-09-09'
Transform: AWS::Serverless-2016-10-31
Description: 'your-email-lambda'
Resources: YourEmailFunction: Type: AWS:Serverless::Function Properties: Policies: - Version: '2012-10-17' Statement: - Effect: Allow Action: - 'ses:SendEmail' - 'ses:SendRawEmail' Resource: '*'As what others said you should add this two permissions: ses:SendEmail,ses:SendRawEmail
I just want to add explaination for those who use Serverless framework
In serverless.yml:
provider: name: aws stage: dev runtime: nodejs10.x region: us-west-1 iamRoleStatements: - Effect: Allow Action: - dynamodb:Query - dynamodb:Scan - dynamodb:GetItem - dynamodb:PutItem - dynamodb:UpdateItem - dynamodb:DeleteItem - lambda:InvokeFunction - ses:SendEmail # add this - ses:SendRawEmail # add this Resource: '*' # add thisIAM Policy fixed the issue. Policy summary will show if there are any warnings i.e. resource does not exist etc.
JSON needs following
{ "Sid": "VisualEditor1", "Effect": "Allow", "Action": [ "ses:SendEmail", "ses:SendRawEmail" ], "Resource": "*" }For Serverless Components yaml:
...
inputs: name: ${name}-${stage} region: ... service: lambda.amazonaws.com policy: - Effect: Allow Action: - ses:SendEmail - ses:SendRawEmail Resource: '*'Solution: You got permission error. your lambda iam identity needs to implement this missing iam policy - right action ( ses:SendEmail ) and right effect ( Allow ) to gain access permissions to this resource ( verified domain - arn ). on terraform you can add the following iam policy:
statement { actions = ["ses:SendEmail"] effect = "Allow" resources = ["arn:aws:ses:us-west-2:XXX:identity/"] sid = "emailFromAWSLambdaServerlessMachine" }As a result - your policy will look like following:
{ "Effect":"Allow", "Action":[ "ses:SendEmail" ], "Resource":"arn:aws:ses:us-west-2:XXX:identity/", "Sid": "emailFromAWSLambdaServerlessMachine"
}P.S try avoid applying * as a resource or an action and limit access as much as possible for mitigate a security risks.
You have to create a policy in order to relate your IAM user with your email sender.
First you have to create the SMTP credentials. In your Account Dashboard go down and select Create SMTP CredentialsWell, now you have the IAM user you are going to use it to send emails with SES. Copy the user ARN (something like this: arn:aws:iam::601688880060:user/ses-smtp-user.20227405-2043453), you will need it in the next step.
In your AWS SES account select your verified email you are going to use to send. Go to the Authorization tab. Create a Policy using the policy generator. There you have to paste there the user ARN. Check the options you want, apply policy.
To finish, add the credentials in your code. (you can also use a file named "credentials" in the ".aws" root directory)
$SesClient = new SesClient([ 'version' => '2010-12-01', 'region' => 'us-east-2', 'credentials' => [ 'key' => 'AKIAYYFKAU4OBNUT', 'secret' => '9B9fuJIQdPFTkq5ZwR4b3OF3NsIAOwYtCv', ],
]);That's it, good luck !
![Where does Hestu go after the first encounter? [duplicate]](https://ly.shilpakalanarail.gov.bd/uploads/where-does-hestu-go-after-the-first-encounter-duplicate_720.jpg)
![Why is there no 4-player pre-made group on Flex Queue? [closed]](https://ly.shilpakalanarail.gov.bd/uploads/why-is-there-no-4-player-pre-made-group-on-flex-queue-closed_720.jpg)