"AADSTS50034: To sign into this application the account must be added to the directory
 Sophia Terry
Sophia Terry 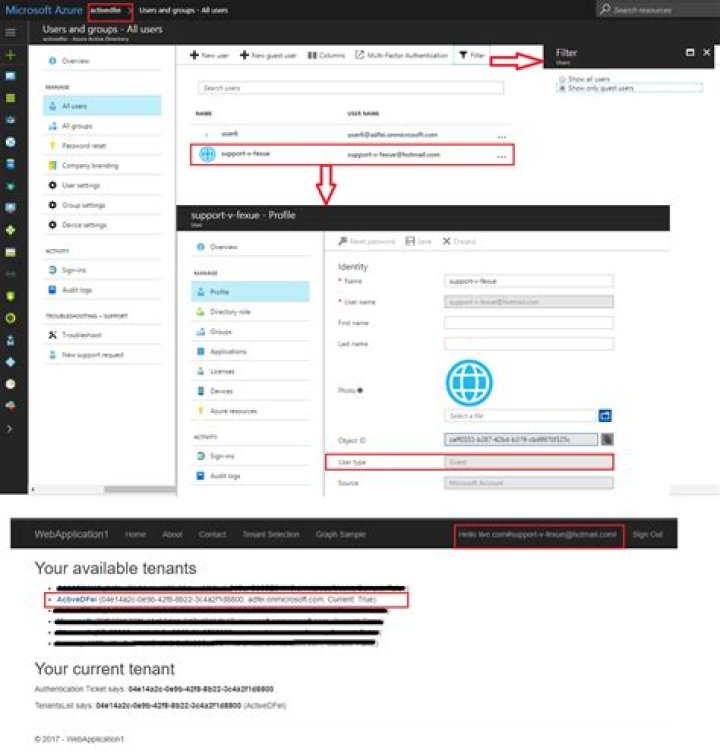
The situation of getting list of tenants of user. When user is logged in directory where he is a member, the exception doesn't occur. Otherwise it does, but this user is assigned to that directory as Guest.
Exception: { "error":"invalid_grant", "error_description":"AADSTS50034: To sign into this application the account must be added to the GUID directory.\r\nTrace ID: GUID\r\nCorrelation ID: GUID\r\nTimestamp: 2017-08-03 14:32:32Z", "error_codes":[50034], "timestamp":"2017-08-03 14:32:32Z", "trace_id":"GUID", "correlation_id":"GUID"
}Stack shows on AcquireTokenSilentAsync.
33 Answers
If you were not developing an multi-tenant app, to get the token from Azure AD the user sign-in should be in that tenant.
And if you were developing an multi-tenant app, we should replace tenant with common in the authorization/token request(refer this link).
Update
4Okay, so I was really curious with what was wrong - and it was actually a mistake I made in the sample (I didn't even notice from the Fiddler logs, what a shame). The issue was that I have been using the common endpoint everywhere for the token cache and obtaining new tokens. This seems to work for Microsoft Account but not for B2B users. I have updated the code sample to include the fixes for the authority URL to always take in the tenant's id instead of the common namespace - which really shouldn't be used anyways. More on that on Vittorio's blog.
try to use User Principal Name instead of email